Our founding team includes operators that have worked in dev tools, fintech, and cybersecurity, so we take security seriously across every aspect of our product and processes.
Schematic has put in place several technical and organizational measures designed to protect data and the application. We are secure by design and practice.
Schematic is SOC 2 Type 1 and Type 2 compliant; we use Vanta to manage our compliance, and work with a reputable auditor for our SOC 2 audits.
Our most recent report is from Feb 14, 2026 and can be provided upon request.
For the full compliance overview, see our Trust Center.
Customer Data is the information you submit to Schematic for processing on your behalf. It includes the identity keys your systems use to refer to a company or user, optional profile traits (name, email, role, or any custom field you send), usage events recorded through the track API, and the subscription state Schematic mirrors from your billing provider.
For the list of third parties that process Customer Data on our behalf, see Subprocessors.
Schematic does not store, process, or transmit payment card data. Schematic leverages Stripe for all payment processing, and Stripe is certified as a PCI Level 1 Service Provider, ensuring industry-standard protection for all payment data.
All customer-facing endpoints require TLS 1.2 or higher, terminated at the load balancer. Data at rest is encrypted with AES-256. API keys and service credentials are stored in encrypted secret stores and are never written to logs. Outbound webhooks are signed, and every Schematic SDK includes helpers for verifying webhook signatures before your application processes them.
API access is segmented by environment and key type. Publishable keys are scoped for client-side SDKs and carry limited authority. Secret keys are used by server-side SDKs and grant the access required to call privileged endpoints. Embedded components render with short-lived JWT session tokens minted on your server, which avoids exposing secret keys to the browser.
Schematic has implemented the following security measures:
Schematic has internal and external monitoring in place to ensure the security of our application.
For all customers, Schematic supports SSO through Google and Github. Additionally, customers can enable 2FA through
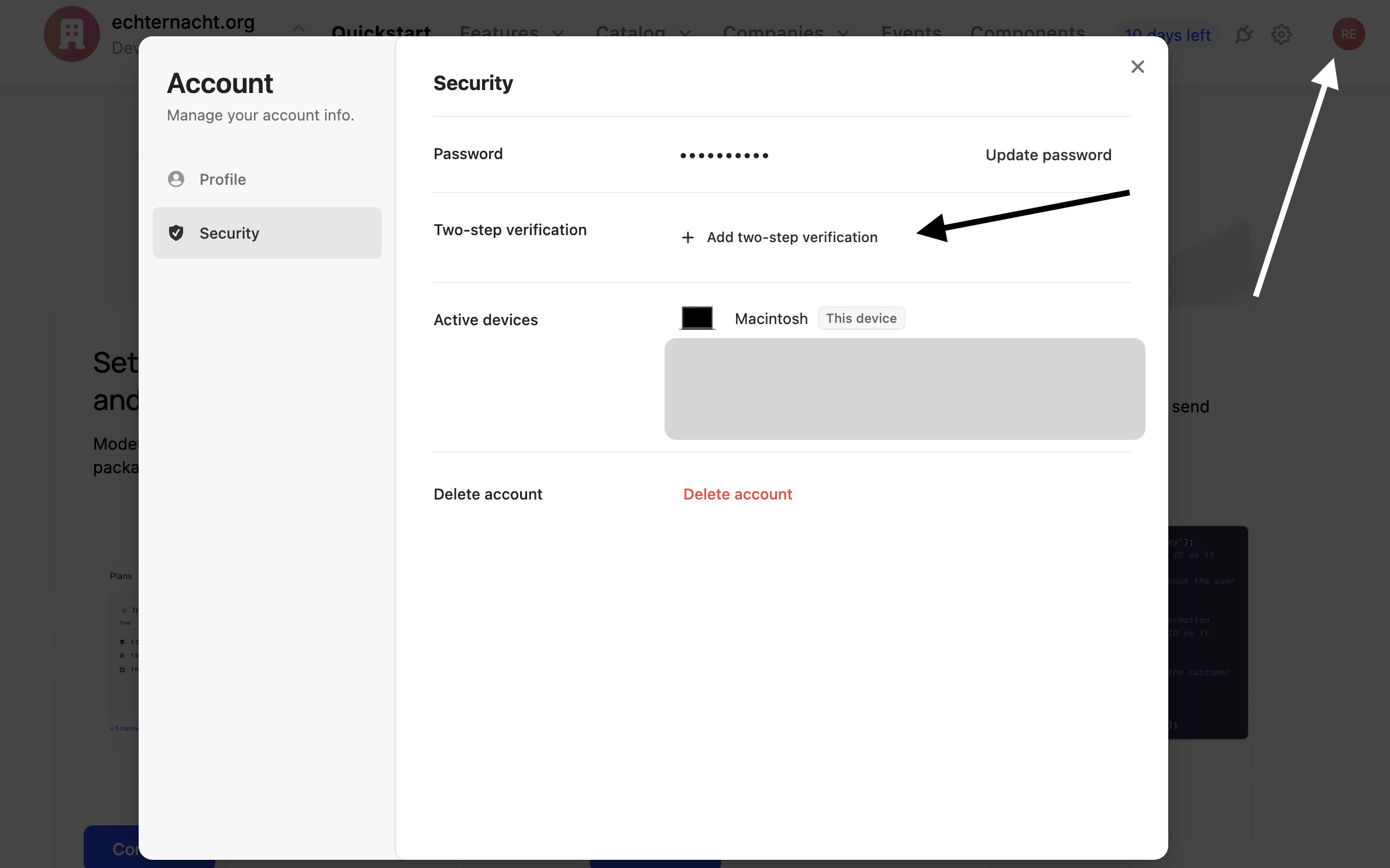
We can also support Custom SSO providers such as Okta, Auth0, etc for customers on the Enterprise plan. If you have any questions, please reach out to us at support@schematichq.com.
Customers are notified within 72 hours of a confirmed incident affecting their Customer Data, in line with the Data Processing Addendum.
We have a number of policies in place to support SOC 2 compliance. All of these policies are available for viewing upon request:
Please report security vulnerabilities or bugs to support@schematichq.com.
We currently do not operate a bug bounty program, but we will be forever grateful for any actionable security vulnerability found and will shower you with thanks and merch.